从其他安全和CDN提供商转换的客户(TCO)在使用Edgio时,平均可节省40%的运营总成本。
- 支持事件更少
- 降低DDoS攻击流量成本
- 通过托管服务缩小团队规模
- 降低软件许可和升级成本
- 降低安全支持,SOC和培训成本
全球金融,电子商务, 和媒体领导者




比较特征
Basic Features
Free
Professional
Enterprise
Premier
Platform Features
Support unmetered delivery of all in-scope application traffic as well as unmetered DDoS protection of all application traffic through Edgio Application Platform.
- Unlimited
- Unlimited
- Unlimited
- Unlimited
Support managing application configuration via the use of RESTful API, Command Line Interface (CLI), and Configuration as Code (Edge JS). Integrates management of services with a variety of developer and operation workflows.
The authoritative DNS is the source of truth for a domain’s DNS records and is the final holder of the domain’s IP address and other DNS records like A, MX and CNAME records. The authoritative DNS is responsible for answering DNS queries with the most accurate data.
Support access to Edgio’s PCI DSS Level 1 compliant network footprints.
Supports setting up SSO with identity provider using SAML to allow login using the credentials stored in customer’s organization’s SAML Identity Provider (IDP).
Support deploying TLS certificates as well as serving customer content from dedicated IP groups for customer applications. Note: While the IP groups are dedicated to a specific customer’s content, the IP addresses are not intended to be static and are subject to change without notice.
Check the Pricing page for feature details.
Security Features
Feature to protect your website & application
Protection from web application and API threats with rulesets automatically maintained and updated by Edgio’s security team.
Offer the ability to analyze rule changes against production traffic without disabling production WAAP rules or affecting legitimate users. Dual WAAP enables faster, more accurate deployment of custom security rules.
API Security provides protection for APIs, using machine learning (ML) to detect APIs while allowing you to manage multiple JSON schemas. API Security also allows you to enforce a positive security model, blocking all requests that do not adhere to the schema, and provides safeguards against sensitive data & code leaks, plus L7 (HTTP/S) DDoS attacks
Secure your web forms and APIs against programmatic attacks. With Bot Manager Standard, Edgio’s high performance bot rules use browser validation to detect malicious automated traffic and prevent it from reaching your web application.
Advanced Bot Management applies machine learning (ML) on top of signature and behavioral fingerprints to detect and mitigate malicious bots while allowing known good bots to do their job.
- Standard
- Standard
- Advanced
- Advanced
Check the Pricing page for feature details.
Observability Features
Observability Features
Real-Time Log Delivery (RTLD) delivers log data in near real-time to a variety of destinations.
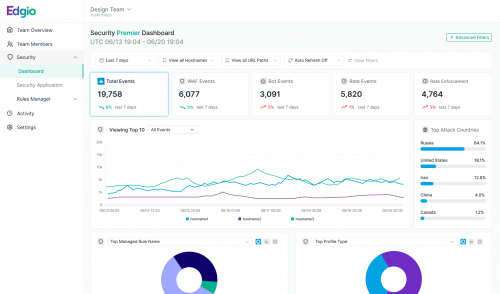
Near real-time and comprehensive reporting for security events.
- 7 Days
- 30 Days
- 60 Days
- 60 Days
Use Edge Insights to gain historical and near real-time insights into threat profiles, performance, and CDN usage.
-
7 Days w/ 6hrs
Full Sampling -
30 Days w/ 12hrs
Full Sampling -
30 days w/ 24hrs
Full Sampling
Our real user monitoring (RUM) library allows real-time tracking of your websites Core Web Vitals for Chromium-based browsers and Firefox.
Check the Pricing page for feature details.
Managed Security Services (SOC) Features
Managed Security Services (SOC) Features
Edgio’s Managed WAF (Web Application Firewall) service provides 24/7 monitoring and management of your Web Application Firewall. As part of this service, our experts will tailor the deployment and configuration of Edgio WAF to your tech stack. By tuning rules to current traffic patterns and threats, we will maximize the performance and security afforded by Edgio WAF. We leverage our security expertise and Threat Intelligence service to create policies, signatures, and rules that protect your web assets against OWASP Top 10 risks including injection attacks, cross-site scripting, broken authentication, and more. Included in the Managed WAF service is ongoing tuning which helps to ensure we block the latest threats while ensuring site availability by minimizing false positives.
The Security Operations Center (SOC) follows a set of custom run books that define the operating procedures for responding to a customer’s threats. Run books are crafted to align seamlessly to each customer’s security needs. The run-book defines rules of engagement specifying customer points of contact, Edgio points of contact, threat severity identification, escalation procedures, and more. Defined run books allow the SOC to respond both efficiently and consistently, facilitating swift resolution during any engagement.
Edgio provides comprehensive services to constantly enhance a robust security posture, including a scheduled monthly review and strategy session led by a designated security architect. This session serves as a point-in-time analysis to assess the current state of affairs and strategic planning for the upcoming month based on expected events, projects, and specific customer needs. The monthly review can include: (1) an examination of potential security gaps based on the customer’s current security configuration, including recommendations to address unprotected assets and strategies to prevent direct to origin attacks, 2) a holistic analysis of current security controls in place to ensure adequate Layer 7 DDoS protections are in place 3) a comprehensive review of active WAAP rulesets to ensure they are current and finetuned to optimal thresholds, minimizing false-positives while maximizing protection from threats, (4) an evaluation of audit policies with recommendations to enhance security posture, and (5) a report on attacks mitigated in the past 30 days, aiding customers in understanding and mitigating the threats they face.
With Dedicated Threat Hunting, Enterprise and Premier customers will get ahead of the curve for protection from zeroday vulnerabilities through rapid deployment of mitigating rules, before those updates are available for GA. The Security Architect assigned to the customer will: (1) Determine if the disclosed vulnerabilities are relevant to the customer’s web properties. (2) Use the suite of WAF tools to mitigate vulnerabilities (custom rules, access rules, rate rules, and bot detection). (3) Identify encoding obfuscation attacks that are specific to the customer’s properties and suggest custom rules to mitigate such attacks.
Dedicated Virtual Patch Support includes custom written WAF signatures to protect application specific vulnerabilities not covered by current Edgio rulesets. This would apply for any zero-day protections outside of publicly disclosed CVEs.
These are on-demand in nature and require iterative testing to ensure no false positives are included.
Check the Pricing page for feature details.
由专家团队管理的保护
威胁情报
网络和安全专家以及先进的ML模型可实时缓解威胁。
托管Web应用程序防火墙(WAF)
Edgio安全专家简化了安全性和性能,使您可以专注于工作。
全天候监控和响应
我们的安全运营团队全天候工作×,在威胁升级之前主动检测和缓解威胁。
全频谱网络安全套件
第3,4和7层DDoS保护
保护您的企业免受第3层,第4层和第7层分布式拒绝服务攻击。
双WAF模式
根据生产流量分析规则更改,而不禁用生产WAF规则或影响合法用户。
高级Bot Manager
借助基于行为指纹的人工智能/机器学习,准确实时拦截恶意爬虫程序。

亚秒级速度的性能特性
图像优化
动态转换图像的大小,以便根据您的网站进行定制。
应用程序规则
确定如何处理特定环境的请求。
预测性预取
通过在用户请求之前预取页面和API调用来加快用户体验。
网站测试和转换工具
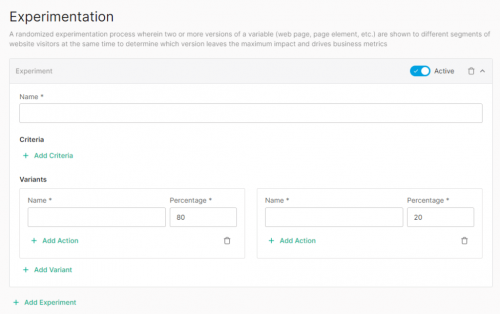
实验
控制Canary部署的流量拆分,执行A/B测试等。
功能标志
在不修改源代码或不需要重新部署的情况下启用或禁用功能。
迭代迁移
在不中断用户体验的情况下安全地迁移到可组合的体系结构。
“我们离开Akamai是因为Edgio为我们节省了大量成本。 此外,还有更新的基础设施和更强大的支持产品。 [Edgio拥有]比竞争对手更好的工具,定价和支持。”
Kyle Rao.
安全医疗总裁
